Quick Start Guide to Breaking Into Systems: The Ultimate Guide for Ethical Hackers and Cyber Security Professionals

5 out of 5
| Language | : | English |
| File size | : | 1572 KB |
| Text-to-Speech | : | Enabled |
| Enhanced typesetting | : | Enabled |
| Print length | : | 127 pages |
| Screen Reader | : | Supported |
In today's digital world, cyber security is more important than ever before. With the increasing number of cyber attacks, it is essential for businesses and individuals to take steps to protect themselves. One of the best ways to do this is to learn how to break into systems. By understanding how hackers operate, you can better protect yourself from their attacks.
This guide will teach you everything you need to know about ethical hacking and cyber security. You will learn how to identify vulnerabilities, exploit them, and protect yourself from cyber attacks. This guide is perfect for beginners who want to learn about ethical hacking as well as experienced professionals who want to brush up on their skills.
Chapter 1: What is Ethical Hacking?
Ethical hacking is the practice of using hacking techniques to identify vulnerabilities in computer systems and networks. Ethical hackers use their skills to help organizations improve their security posture. They do not use their skills for malicious purposes, such as stealing data or damaging systems.
There are many different types of ethical hacking, including:
- Penetration testing: This involves simulating a real-world attack to identify vulnerabilities in a system.
- Vulnerability assessment: This involves identifying vulnerabilities in a system without actually exploiting them.
- Exploit development: This involves creating tools and techniques to exploit vulnerabilities in systems.
- Security assessment: This involves evaluating the overall security of a system, including its hardware, software, and network configuration.
Chapter 2: How to Get Started with Ethical Hacking
If you are interested in becoming an ethical hacker, there are a few things you need to do to get started.
- Learn the basics of computer systems and networks.
- Install a virtual machine on your computer.
- Learn a programming language.
- Get involved in the ethical hacking community.
Chapter 3: Identifying Vulnerabilities
The first step in ethical hacking is to identify vulnerabilities in a system. There are many different ways to do this, including:
- Scanning: This involves using tools to automatically scan a system for vulnerabilities.
- Manual testing: This involves manually testing a system for vulnerabilities.
- Social engineering: This involves using psychological techniques to trick people into revealing information or taking actions that could compromise a system.
Chapter 4: Exploiting Vulnerabilities
Once you have identified vulnerabilities in a system, you can exploit them to gain access to the system. There are many different ways to exploit vulnerabilities, including:
- Buffer overflows: This involves sending more data to a system than it can handle, which can cause the system to crash.
- SQL injection: This involves inserting malicious SQL code into a web application, which can allow an attacker to access sensitive data.
- Cross-site scripting (XSS): This involves injecting malicious JavaScript code into a web application, which can allow an attacker to steal cookies or hijack a user's session.
Chapter 5: Protecting Yourself from Cyber Attacks
Once you have learned how to break into systems, it is important to learn how to protect yourself from cyber attacks. There are many things you can do to protect yourself, including:
- Use strong passwords.
- Keep your software up to date.
- Be careful about what you click on.
- Use a firewall.
- Backup your data.
This guide has provided you with a comprehensive overview of ethical hacking and cyber security. You have learned how to identify vulnerabilities, exploit them, and protect yourself from cyber attacks. This guide is just the beginning of your journey into the world of ethical hacking. There are many more resources available to help you learn more about this fascinating and rewarding field.
Remember, ethical hacking is a powerful tool that can be used to protect yourself and your organization from cyber attacks. By learning how to break into systems, you can better understand how to protect yourself from them.
Additional Resources
- OWASP
- SANS
- SecurityFocus
5 out of 5
| Language | : | English |
| File size | : | 1572 KB |
| Text-to-Speech | : | Enabled |
| Enhanced typesetting | : | Enabled |
| Print length | : | 127 pages |
| Screen Reader | : | Supported |
Do you want to contribute by writing guest posts on this blog?
Please contact us and send us a resume of previous articles that you have written.
 Book
Book Novel
Novel Page
Page Chapter
Chapter Text
Text Story
Story Genre
Genre Reader
Reader Library
Library Paperback
Paperback E-book
E-book Magazine
Magazine Newspaper
Newspaper Paragraph
Paragraph Sentence
Sentence Bookmark
Bookmark Shelf
Shelf Glossary
Glossary Bibliography
Bibliography Foreword
Foreword Preface
Preface Synopsis
Synopsis Annotation
Annotation Footnote
Footnote Manuscript
Manuscript Scroll
Scroll Codex
Codex Tome
Tome Bestseller
Bestseller Classics
Classics Library card
Library card Narrative
Narrative Biography
Biography Autobiography
Autobiography Memoir
Memoir Reference
Reference Encyclopedia
Encyclopedia Stith Thompson
Stith Thompson Rob Rose
Rob Rose Rachel Allen
Rachel Allen Susan Quayle
Susan Quayle Theodore Dimon
Theodore Dimon Rich Brownstein
Rich Brownstein Richard James Burgess
Richard James Burgess Warren E Levinson
Warren E Levinson Shazzie
Shazzie Robert Bevan
Robert Bevan Stefan Stenudd
Stefan Stenudd Steven Otfinoski
Steven Otfinoski Sandeep Balakrishna
Sandeep Balakrishna R Mark Hall
R Mark Hall Richard Gordon
Richard Gordon Rui Canossa
Rui Canossa Ron Jenkins
Ron Jenkins Rose Verde
Rose Verde Ryan A Pedigo
Ryan A Pedigo Shannon Vallor
Shannon Vallor
Light bulbAdvertise smarter! Our strategic ad space ensures maximum exposure. Reserve your spot today!
 Christian CarterCatherine Gift Krasnodar Russia Rob In Russia - An Unforgettable Journey to...
Christian CarterCatherine Gift Krasnodar Russia Rob In Russia - An Unforgettable Journey to...
 Patrick RothfussUn Simpatico Libro Con Cui Bambini Possono Guardare Diverse Figure Trovare: A...
Patrick RothfussUn Simpatico Libro Con Cui Bambini Possono Guardare Diverse Figure Trovare: A...
 Jesus MitchellLearn 000 Basic Korean Words And Phrases Quickly And Easily Hangul Romanized
Jesus MitchellLearn 000 Basic Korean Words And Phrases Quickly And Easily Hangul Romanized Israel BellFollow ·14.2k
Israel BellFollow ·14.2k Jacob FosterFollow ·19.7k
Jacob FosterFollow ·19.7k Alan TurnerFollow ·18.3k
Alan TurnerFollow ·18.3k Griffin MitchellFollow ·3.6k
Griffin MitchellFollow ·3.6k Pete BlairFollow ·15k
Pete BlairFollow ·15k Earl WilliamsFollow ·11.2k
Earl WilliamsFollow ·11.2k Shannon SimmonsFollow ·4.8k
Shannon SimmonsFollow ·4.8k Howard PowellFollow ·14.2k
Howard PowellFollow ·14.2k
 Eli Brooks
Eli BrooksOver 700 Organic Remedies Shortcuts And Tips For The...
: Embracing the Power of...
 Carter Hayes
Carter HayesUnveiling the Unofficial Political Religion of India: A...
Embark on an...
 Colin Richardson
Colin RichardsonOf Colors and Critters: A Journey Through the Animal...
In the tapestry of...
 Harry Hayes
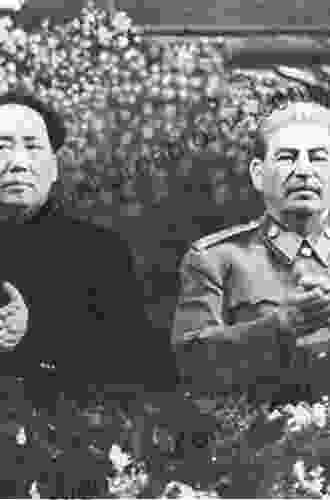
Harry HayesUnveiling the Hidden Truths: Mao, Stalin, and the Korean...
Step into the enigmatic realm of the 20th...
 George Bernard Shaw
George Bernard ShawBand 1b Pink: A Journey Through the World of Reading
Band 1b Pink is a...
5 out of 5
| Language | : | English |
| File size | : | 1572 KB |
| Text-to-Speech | : | Enabled |
| Enhanced typesetting | : | Enabled |
| Print length | : | 127 pages |
| Screen Reader | : | Supported |